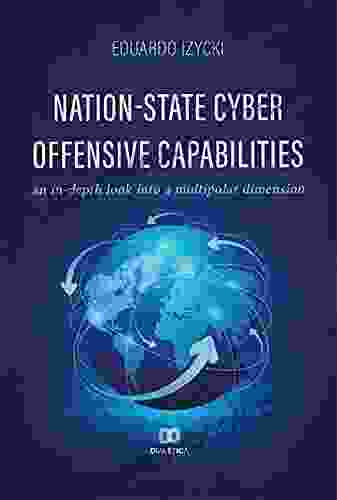
Exploring the Evolving Landscape of Nation-State Cyber Offensive Capabilities: A Comprehensive Analysis

In the digital era, nation-states have emerged as key players in the realm of cyber offense. As technology continues to advance at an unprecedented pace, so too have the capabilities and tactics employed by governments seeking to gain strategic advantages in cyberspace. This article aims to provide a comprehensive analysis of nation-state cyber offensive capabilities, exploring their evolution, tactics, and implications for global cybersecurity.
Evolution of Nation-State Cyber Offensive Capabilities
The history of nation-state cyber offense can be traced back several decades, with the advent of the internet and the proliferation of digital infrastructure. Initially, cyberattacks were primarily conducted by individuals or groups seeking financial gain or disruption. However, as governments recognized the potential of cyberspace as a strategic domain, they began investing in the development of offensive cyber capabilities.
4.7 out of 5
| Language | : | English |
| File size | : | 28157 KB |
| Text-to-Speech | : | Enabled |
| Enhanced typesetting | : | Enabled |
| Print length | : | 307 pages |
| Screen Reader | : | Supported |
In the early 2000s, nation-states began developing their own cyberwarfare programs, establishing specialized units dedicated to conducting offensive operations in cyberspace. Initially, these programs focused on traditional cyberattacks, such as denial-of-service attacks and website defacements. However, as technology advanced, nation-states developed more sophisticated capabilities, including:
- Advanced Persistent Threats (APTs): Long-term and stealthy cyberattacks designed to penetrate and maintain a presence within target networks.
- Zero-day exploits: Vulnerabilities in software or hardware that are unknown to the vendor and can be exploited to gain unauthorized access or control.
- Stuxnet: A highly sophisticated malware specifically designed to target Iran's nuclear program, demonstrating the destructive potential of cyber offense.
Tactics Employed by Nation-States
Nation-states employ a wide range of tactics in their cyber offensive operations, including:
- Espionage: Stealing sensitive information from foreign governments, businesses, or individuals.
- Sabotage: Disrupting or disabling infrastructure, such as power grids or communication networks.
- Influence operations: Using social media, disinformation campaigns, and other tactics to manipulate public opinion or undermine political stability.
- Cyberwarfare: Using cyberattacks to directly attack military systems or infrastructure.
Implications for Global Cybersecurity
The evolution of nation-state cyber offensive capabilities raises serious concerns for global cybersecurity. These attacks can have devastating consequences, including:
- Economic damage: Disrupting critical infrastructure or stealing sensitive business情報を can lead to significant financial losses.
- National security risks: Cyberattacks can compromise military systems or leak sensitive information, threatening national security.
- Loss of privacy: Espionage and surveillance operations can侵害 the privacy of individuals and organizations.
Countering Nation-State Cyber Offense
Countering nation-state cyber offensive capabilities requires a multi-faceted approach, including:
- Strengthening cybersecurity defenses: Implementing robust security measures, such as firewalls, intrusion detection systems, and security awareness training, can help prevent and mitigate cyberattacks.
- International cooperation: Collaborating with other governments and international organizations can facilitate the sharing of intelligence, best practices, and resources to combat cyber threats.
- Developing norms of responsible behavior: Establishing clear guidelines for acceptable behavior in cyberspace can help prevent escalation and reduce the risk of conflict.
- Addressing the underlying causes: Tackling the socioeconomic and political factors that can contribute to cyber conflict can help reduce the likelihood of attacks.
Nation-state cyber offensive capabilities are a rapidly evolving threat to global cybersecurity. The sophisticated tactics and destructive potential of these attacks highlight the need for continued vigilance and cooperation among governments, businesses, and individuals. By strengthening defenses, promoting international collaboration, and addressing the underlying causes of cyber conflict, we can create a more secure and stable cyberspace for all.
4.7 out of 5
| Language | : | English |
| File size | : | 28157 KB |
| Text-to-Speech | : | Enabled |
| Enhanced typesetting | : | Enabled |
| Print length | : | 307 pages |
| Screen Reader | : | Supported |
Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
 Top Book
Top Book Novel
Novel Fiction
Fiction Nonfiction
Nonfiction Literature
Literature Paperback
Paperback Hardcover
Hardcover E-book
E-book Audiobook
Audiobook Bestseller
Bestseller Classic
Classic Mystery
Mystery Thriller
Thriller Romance
Romance Fantasy
Fantasy Science Fiction
Science Fiction Biography
Biography Memoir
Memoir Autobiography
Autobiography Poetry
Poetry Drama
Drama Historical Fiction
Historical Fiction Self-help
Self-help Young Adult
Young Adult Childrens Books
Childrens Books Graphic Novel
Graphic Novel Anthology
Anthology Series
Series Encyclopedia
Encyclopedia Reference
Reference Guidebook
Guidebook Textbook
Textbook Workbook
Workbook Journal
Journal Diary
Diary Manuscript
Manuscript Folio
Folio Pulp Fiction
Pulp Fiction Short Stories
Short Stories Fairy Tales
Fairy Tales Fables
Fables Mythology
Mythology Philosophy
Philosophy Religion
Religion Spirituality
Spirituality Essays
Essays Critique
Critique Commentary
Commentary Glossary
Glossary Bibliography
Bibliography Index
Index Table of Contents
Table of Contents Preface
Preface Introduction
Introduction Foreword
Foreword Afterword
Afterword Appendices
Appendices Annotations
Annotations Footnotes
Footnotes Epilogue
Epilogue Prologue
Prologue Lynsay Sands
Lynsay Sands Jalal Al Din Rumi
Jalal Al Din Rumi John Inman
John Inman Angela Grassi
Angela Grassi Imani Perry
Imani Perry Miranda Cowley Heller
Miranda Cowley Heller Samuel Beckett
Samuel Beckett Thea Cambert
Thea Cambert Joan Wolf
Joan Wolf Timothy Beal
Timothy Beal James V Mcconnell
James V Mcconnell Sampat Daniel
Sampat Daniel Tea Cooper
Tea Cooper Ana Elena Pena
Ana Elena Pena Elle Charles
Elle Charles Alex Grecian
Alex Grecian Sophie Jordan
Sophie Jordan Thankgod Adoyi Ocheme
Thankgod Adoyi Ocheme Julia Donaldson
Julia Donaldson Michele Gilcrest
Michele Gilcrest
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 Jake CarterOn Love: A Deep Dive into the Turbulent World of Charles Bukowski's Romantic...
Jake CarterOn Love: A Deep Dive into the Turbulent World of Charles Bukowski's Romantic... William WordsworthFollow ·11.6k
William WordsworthFollow ·11.6k Stanley BellFollow ·15.8k
Stanley BellFollow ·15.8k Dashawn HayesFollow ·4.4k
Dashawn HayesFollow ·4.4k Howard BlairFollow ·12.4k
Howard BlairFollow ·12.4k Ray BlairFollow ·3.8k
Ray BlairFollow ·3.8k Octavio PazFollow ·6.4k
Octavio PazFollow ·6.4k Tennessee WilliamsFollow ·17.9k
Tennessee WilliamsFollow ·17.9k Ernest J. GainesFollow ·17.5k
Ernest J. GainesFollow ·17.5k
 Dean Cox
Dean CoxHow to Make Decisions Easily & Effortlessly: The...
The Different Types of Decisions There...
 Gustavo Cox
Gustavo CoxThe End of World War II and the Birth of Baseball's...
The end of...
 Patrick Rothfuss
Patrick RothfussThe Dantes: An 11-Family Saga of Billionaires, Soulmates,...
The Dantes is an epic family saga that follows...
 Dylan Mitchell
Dylan MitchellSuper Friends: The Animated Adventures That Defined a...
In the vibrant landscape of American...

 Jamal Blair
Jamal BlairCollege For Students With Disabilities: We Do Belong
College can be a...
4.7 out of 5
| Language | : | English |
| File size | : | 28157 KB |
| Text-to-Speech | : | Enabled |
| Enhanced typesetting | : | Enabled |
| Print length | : | 307 pages |
| Screen Reader | : | Supported |